What is the Internet of Things? background of IoT
Digital Ritesh
Background of IoT
The term Internet of Things (IoT) was used for the first time by Kevin Ashton in 1999 while holding a presentation at Proctor & Gamble.
He used the term to link the idea of radio frequency identification (RFID) to the then-new topic Internet.
Since then the use of this term has blossomed and major companies have predicted an increase in IoT.
The reason IoT has become so huge depends partly on two things: Moore’s law and Koomey’s law.
Moore’s law states that,
The number of transistors on a chip doubles approximately every two years.
This has enabled people to develop more powerful computers on the same sized chip.
Koomey’s law explains that,
The number of computations per kilowatt-hour roughly doubles every one and a half years.
Kevin Ashton states that these two laws have together enabled us to create powerful and energy-efficient computers.
By turning the graph for Moore’s law upside down it can be interpreted as the size of a computer is halved every two years.
Doing the same thing to Koomey’s law can be interpreted as the amount of energy needed to perform a computation dropping at a rapid rate.
Combining these interpretations tells us that we can perform the same amount of computations on an increasingly smaller chip while consuming decreasing amounts of energy.
The potential result is a small, powerful, and energy-efficient computer that enables us to provide more advanced services using less chip area and at lower energy than what has been possible before.
Defining the term IoT can be somewhat difficult, the basic concept of IoT is to connect things together, thus enabling these “things” to communicate with each other and enabling people to communicate with them.
A global infrastructure for the information society, enabling advanced services by interconnecting (physical and virtual) things based on existing and evolving interoperable information and communication technologies.
That is the definition of IoT proposed by ITU’s Telecommunication Standardization Sector.
Interconnecting the physical world with the virtual world and applying this concept to all things opens up new possibilities in the sense of being able to at any time access anything from any place.
“Things” in the physical world are objects that physically exist and from the perspective of IoT, we are able to sense, operate, and connect to these things, while in the virtual world “things” are objects that can be stored, accessed, and processed.
IoT involves sensors in order to collect information, sensors are already being used in daily life, and smartphones contain different kinds of sensors, such as accelerometers, cameras, and GPS.
Built-in sensors are nothing new in today’s society. IoT is already happening but might be not seen compared to smartphones which can both be seen and touched.
IoT technology already exists but is not necessarily seen, so the development of IoT might progress a long way before it is visible to everyone.
The most vital part of achieving IoT is communication because in order to interconnect different devices they must be able to communicate.
There are some fundamental characteristics of IoT that provide a clearer picture of the actual differences between IoTs and other devices:
• Interconnectivity: Everything can be connected to the global information and communication infrastructure, it is the basic characteristic of IoT.
• Things-related services: Things-related services resolves around devices being constrained by their CPU performance, memory, and power which limits what a device can do when it can do it, and how often it can do it.
• Heterogeneity: Devices within IoT have different hardware and use different networks but they can still interact with other devices through different networks.
Supporting heterogeneity is the biggest challenge because there are a lot of different protocols in use.
Interacting through multiple networks will be challenging from both security and technical perspectives, therefore, there are some requirements relevant for IoT, such as security and privacy protection.
Security includes privacy considerations since data collected by for instance a sensor might contain information that is sensitive personal information.
A thing that reports a geographical location can for privacy reasons add noise to its position, thus the physical location compared to the virtual location can differ.
This prevents the device from having an exact location mapped to it thus protecting spatial privacy.
• Dynamic changes: The state of a device can change dynamically, thus the number of devices can vary. (Device states: connected, disconnected, waking up, and sleeping)
• Enormous scale: The number of devices operating and communicating will be larger than the number of devices on the current Internet. Most of this communication will be device to device instead of human to the device.
What is IoT?
IoT includes different objects with different capabilities, which have a common way of communicating for enabling the transfer of information, where this information is understood by two or more objects in order to make a process more efficient.
Objects include both virtual and physical objects, but are not limited to:
- Electronic devices such as computers
- Mobile phones
- televisions
- machines
- robots;
Sensors communication includes Different protocols and technologies for sending digital or analog signals through nodes,
- Constrained Application Protocol
- File Transfer Protocol
- Hypertext Transfer Protocol
- Local Area Networks
- Wide Area Networks
- Body Area Networks
- Wi-Fi
- Ethernet
- fibre optic links
- radio
Capabilities include:
- Gathering information
- processing information
- storing information
- presenting the information.
A process could include:
- Tracking health information
- heating your home
- lighting public streets
- keeping track of assets
An example of non-IoT is a single object speaking its own language and potentially connected to a communication network, but no other object is able to interpret this data and therefore no other object can contribute with any functionality to this non-IoT device.
The contexts in which the term IoT is being used are very different, such as the body, homes, cities, industry, and the global environment.
• In terms of the body, IoT enables sensing and connectivity, for example tracking activity, health status, and other relevant information could improve not only the user’s daily life, but also their future health by preventing bad habits.
• When talking about the home, IoT is often considered in terms of remote and local monitoring and management of different home electronics and lights, or simply to keep plants in the yard alive by using an automatic watering system.
• In correlation to cities, the term IoT is used to describe systems that effectively gather and process information generated by various infrastructures, for example, monitoring centers for traffic lights, street lights, camera surveillance, and the power grid. These systems offer the potential to improve the flow of vehicles and people through the city centers and also greatly improve the energy efficiency of transport systems, while also improving personal and societal safety.
• Optimizations of operations, boosting productivity, saving resources, and reducing costs are typically the main goals of IoT solutions applied in the industry. For example, the industry might use IoT to keep track of business assets, improve environmental safety, and maintain quality and consistency in a production process.
• Last, but not least important, is environmental monitoring where IoT can help us understand and better manage those resources we have. Sensors can help protect wildlife, track water usage and flows, monitor local weather, monitor the use of natural resources, or give warnings before and after natural disasters to prepare people for what is to come.
The ITU-T has defined a reference model for IoT. This model is divided into the four layers:
- application layer
- service and application support layer,
- network layer
- device layer.
Each one of these layers also includes management and security capabilities. These capabilities have both generic and specific capabilities that can cut across multiple layers.
• The application layer contains IoT applications that require certain support capabilities from the underlying layer to function.
• The service and application support layer consists of generic support capabilities which can be used by IoT applications, examples of such capabilities could be data processing or storage. The specific support capabilities are those other than the generic capabilities which are required to create support for diversified applications.
• The network layer is divided into networking and transport capabilities. The networking capabilities provide relevant control functions for network connectivity, while the transport capabilities focus on the transport of IoT services and application-specific data.
• The device layer is where the device capabilities include direct and indirect interaction with the communication network. Unlike direct interaction, indirect interaction requires a gateway to be able to send and receive information via the network.
Two other capabilities are ad hoc networking and sleeping and waking up which enable devices to connect in an ad hoc manner and save energy.
The device layer also includes gateway capabilities to support devices connected via different types of wired and wireless technologies by supporting multiple interfaces.
In some situations, protocol conversion is needed to support communication between devices using different protocols at the device and network layer.
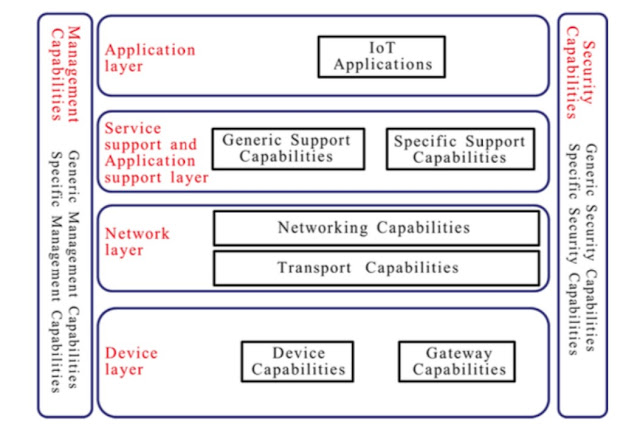 |
| ITU-T reference model |
Generic management capabilities include device management, such as remote device activation, de-activation, diagnostics, and firmware or software updates, and local network topology, traffic, and congestion management.
The generic security capabilities are independent of the application and include authorization and authentication at the application, network, and device layer.
Moreover, all of the layers have their own individual capabilities.
• At the application layer: application data confidentiality and integrity protection, privacy protection, security audit, and anti-virus;
• At the network layer: signaling data confidentiality and integrity protection;
• At the device layer: device integrity validation, access control, data confidentiality, and integrity protection.
Also Read,
What is Digital Marketing? Where to start?
How Digital Marketing Became the Best
Digital marketing vs traditional marketing
The digital advertising, a continuous disruption
How to grow your business with email marketing
Data Needed in Digital Advertising
Predictive Models of Data in Digital Advertising | Digital Ritesh







0 Comments